Why your business requires a General Cybersecurity Assessment
The Importance of General Cybersecurity Assessments for Every Business
Businesses of all sizes are increasingly reliant on technology to streamline operations, enhance customer experiences, and drive growth. However, this reliance comes with a critical downside: the heightened risk of cyber threats. From data breaches to ransomware attacks, businesses are under constant threat.
Performing a general cybersecurity assessment is not just a good practice—it is an essential strategy to safeguard sensitive data, maintain business continuity, and protect a company’s reputation. Many times it is required for compliance adherence. DAG Tech’s CxO Program can perform general cybersecurity assessment for your organization. Contact us today to get started!
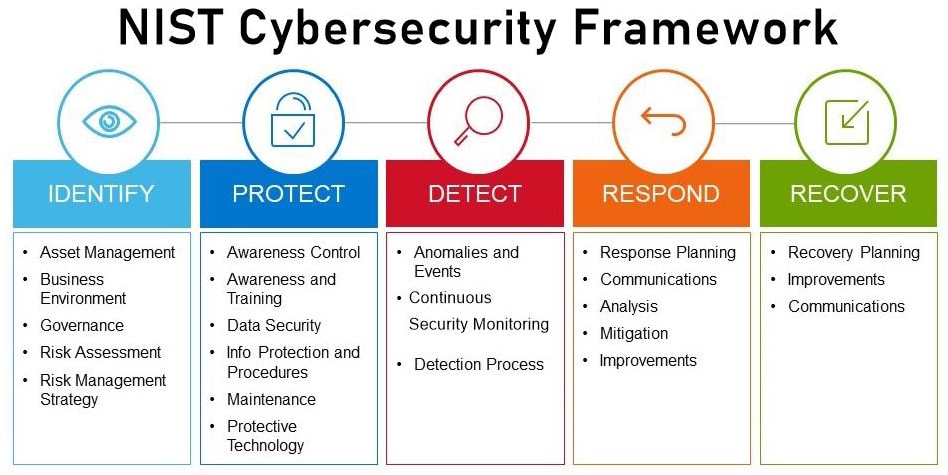
see the NIST Cybersecurity Framework
Here’s why every business should prioritize general cybersecurity assessments:
1. Identifying Vulnerabilities Before They’re Exploited
A cybersecurity assessment acts as a comprehensive health check for your IT systems. It identifies weak points, such as outdated software, misconfigured firewalls, or unpatched vulnerabilities, that could be exploited by hackers. These assessments simulate potential attacks, providing a clear picture of where your organization is most at risk. Proactively addressing these vulnerabilities prevents them from becoming entry points for cybercriminals.
2. Protecting Sensitive Data
For businesses handling sensitive data—whether it’s customer information, financial records, or intellectual property—data protection is paramount. Cybersecurity assessments ensure that data is adequately safeguarded against unauthorized access, leaks, or loss. By evaluating access controls, encryption practices, and data storage policies, businesses can significantly reduce the risk of data breaches.
Regulatory Compliance:
Industries such as healthcare (HIPAA), finance (PCI DSS), and others have stringent data protection regulations. Regular cybersecurity assessments help businesses comply with these regulations, avoiding hefty fines and legal complications.
3. Enhancing Business Continuity
A cyberattack can disrupt business operations, leading to downtime and financial losses. Ransomware attacks, for example, can lock businesses out of their critical systems until a ransom is paid—sometimes with no guarantee of data recovery. Cybersecurity assessments evaluate an organization’s incident response plan, backup solutions, and disaster recovery processes to ensure business continuity in the event of an attack.
Mitigating Risks:
By conducting regular assessments, businesses can develop robust contingency plans and reduce the time needed to recover from a cybersecurity incident.
4. Building Trust with Customers and Partners
Customers and business partners expect their sensitive data to be handled securely. A data breach can erode trust and damage relationships, leading to lost business and reputational harm. By performing regular cybersecurity assessments and addressing any identified issues, businesses demonstrate a commitment to protecting their stakeholders.
Competitive Advantage:
In a competitive market, showcasing strong cybersecurity measures can be a unique selling point. A business that prioritizes cybersecurity is more likely to earn customer loyalty and attract partnerships.
5. Keeping Pace with Evolving Threats
The cybersecurity landscape is constantly evolving. New malware, phishing schemes, and sophisticated hacking techniques emerge daily. A cybersecurity assessment helps businesses stay ahead by identifying new threats and updating their defenses accordingly. Static security measures are no match for dynamic threats, making regular assessments a necessity.
Emerging Threats:
Recent trends, such as supply chain attacks and AI-powered cybercrime, highlight the need for businesses to regularly reassess their security posture.
6. Cost-Effectiveness of Proactive Measures
The cost of a cybersecurity assessment pales in comparison to the financial and reputational damage caused by a successful cyberattack. Downtime, lost revenue, legal fees, and recovery costs can cripple a business. Investing in proactive cybersecurity assessments saves money by reducing the likelihood of costly breaches.
ROI of Cybersecurity:
A well-executed assessment uncovers inefficiencies in existing security measures, enabling businesses to allocate resources more effectively and maximize their cybersecurity ROI.
7. Addressing Human Error
Human error remains one of the leading causes of cybersecurity breaches. Employees clicking on phishing links, using weak passwords, or mishandling sensitive data can all compromise an organization’s security. A general cybersecurity assessment includes evaluating employee awareness and training programs to mitigate risks stemming from human error.
Employee Training:
Cybersecurity assessments often recommend tailored training sessions to help employees recognize and respond to potential threats, strengthening the organization’s overall security posture.
8. Meeting Insurance Requirements
Cybersecurity insurance is becoming a standard component of risk management for businesses. However, insurers often require businesses to meet specific security standards before issuing a policy. Regular cybersecurity assessments demonstrate due diligence and help businesses qualify for coverage.
Reduced Premiums:
Businesses with strong cybersecurity measures are less likely to experience breaches, which can result in lower insurance premiums.
9. Aligning Cybersecurity with Business Goals
A general cybersecurity assessment not only highlights vulnerabilities but also ensures that cybersecurity measures align with overall business objectives. For instance, businesses looking to adopt cloud-based solutions or expand into new markets can use assessment results to address potential security challenges associated with these goals.
Strategic Planning:
Cybersecurity assessments provide actionable insights that help businesses make informed decisions about technology investments and operational changes.
10. Avoiding Legal and Regulatory Consequences
Failure to secure sensitive data can result in legal actions, regulatory fines, and loss of licenses. Cybersecurity assessments evaluate compliance with applicable laws and standards, helping businesses avoid these consequences.
Steps in Conducting a Cybersecurity Assessment
- Identify Assets: Determine what needs protection, including systems, networks, and data.
- Evaluate Threats: Analyze potential threats, such as malware, insider threats, or natural disasters.
- Assess Vulnerabilities: Identify weaknesses in existing security measures.
- Test Controls: Evaluate the effectiveness of firewalls, antivirus software, and access controls.
- Review Policies: Ensure security policies and procedures are up-to-date and effective.
- Implement Recommendations: Address vulnerabilities and improve security measures based on assessment findings.
DAG Tech can be reached through our Request IT Services Form or at 1-888-566-8118.



