How to Deploy Identity Credential and Access Management (ICAM)
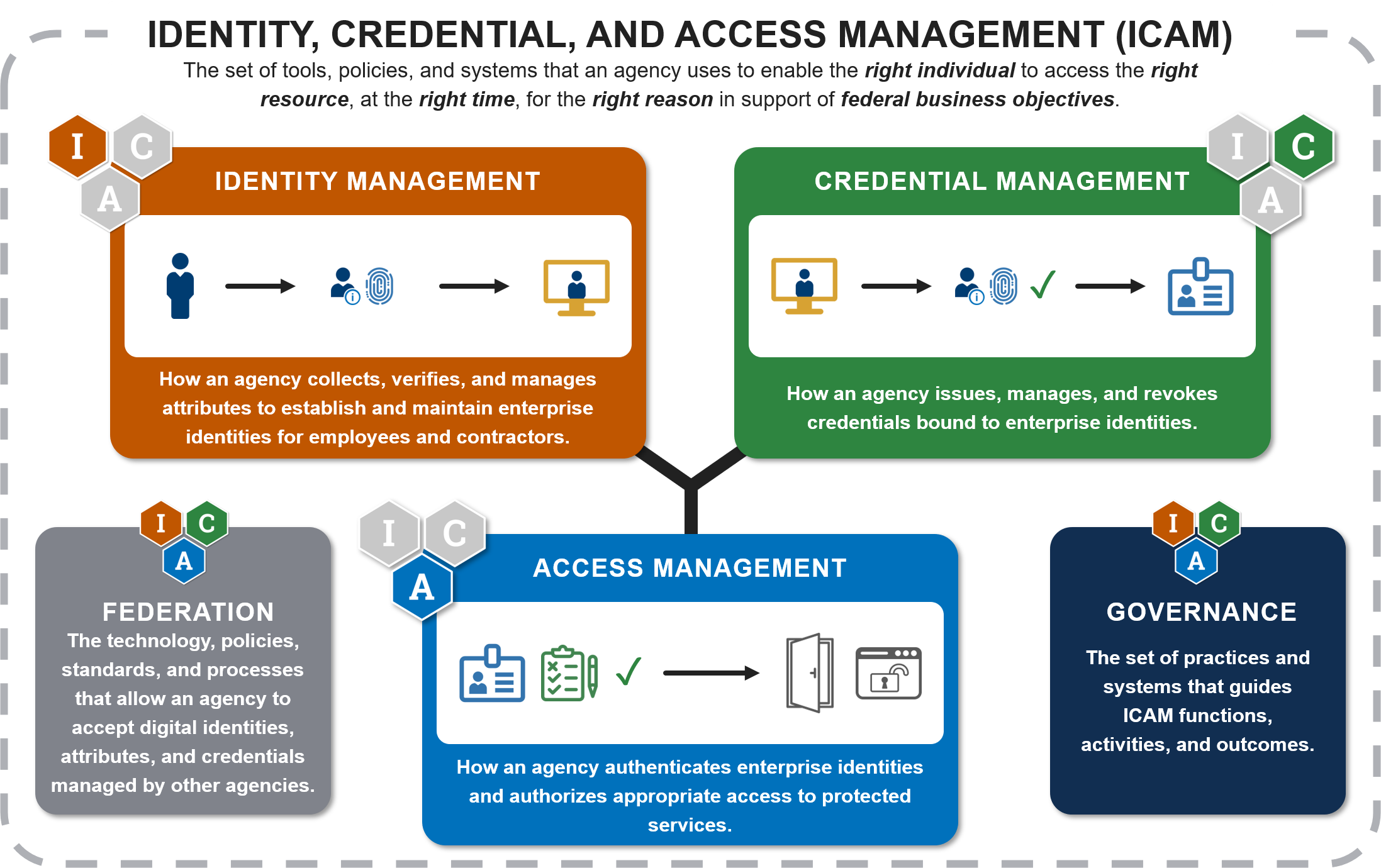
Safeguarding identities and controlling access are paramount to protecting organizational assets. Identity, Credential, and Access Management (ICAM, sometimes referred to as IAM) systems provide a structured approach to managing user identities, authenticating credentials, and authorizing access to information systems. A strong ICAM strategy enables secure interoperability, improves user experience, supports regulatory compliance, and reduces cybersecurity risks. ICAM is a key component of zero-trust architectures and is critical for ensuring that the right people have access to the right information at the right time.
DAG Tech is uniquely positioned to help organizations design, deploy, and optimize their ICAM programs. With our proven methodologies and broad expertise across IT modernization, cybersecurity, and compliance, DAG Tech supports clients from initial assessment to full operational capability. In this blog, we outline how we help organizations deploy ICAM systems — including Federated Identity Management — and how our customized roadmaps and implementation guidance ensure success.
See some leading Federal ICAM (FICAM) Guidelines:
- National Institute of Standards and Technology (NIST) Special Publication (SP) 800-63 Digital Identity Guidelines
- Federal CIO Council Information Security and Identity Management Committee FICAM Ecosystem
- Federal Information Processing Standard 201 (FIPS 201) Evaluation Program also known as the FICAM Testing Program
- Federal Information Security Modernization Act (FISMA) Evaluation Report and directives
- US General Services Administration Identity, Credentialing, and Access Management (ICAM) Solutions and Shares Services Roadmap
Understanding ICAM and Federation
Before discussing the implementation process, it’s important to understand the key components of ICAM:
- I – Identity Management: Governing the lifecycle of digital identities, from creation to deactivation.
- C – Credential Management: Issuing and maintaining secure credentials, such as passwords, smart cards, or biometrics.
- A – Access Management: Controlling user access to resources based on roles, policies, and security standards.
- M – Federated Identity Management: Enabling users to use a single digital identity across multiple organizations or systems, facilitating seamless and secure access without redundant account management.
Federation is critical for organizations collaborating with partners, subsidiaries, and external agencies. It reduces administrative overhead, total cost of ownership, and enhances user experience while maintaining robust security protocols.
How DAG Tech Supports ICAM Deployments
At DAG Tech, our approach to ICAM is both strategic and practical. We ensure that organizations not only deploy technically sound solutions but also align those solutions with broader business goals, compliance requirements, and cybersecurity frameworks.
1. Initial Assessment and Requirements Gathering
Every successful ICAM deployment begins with a comprehensive discovery process. DAG Tech works with stakeholders to:
- Understand business objectives and security requirements.
- Assess existing identity systems, policies, and infrastructure.
- Identify compliance obligations, such as FISMA, NIST SP 800-63, or GDPR.
- Define user groups, system interactions, and access needs.
We perform gap analyses against industry standards and recommend improvements that align with best practices and emerging trends.
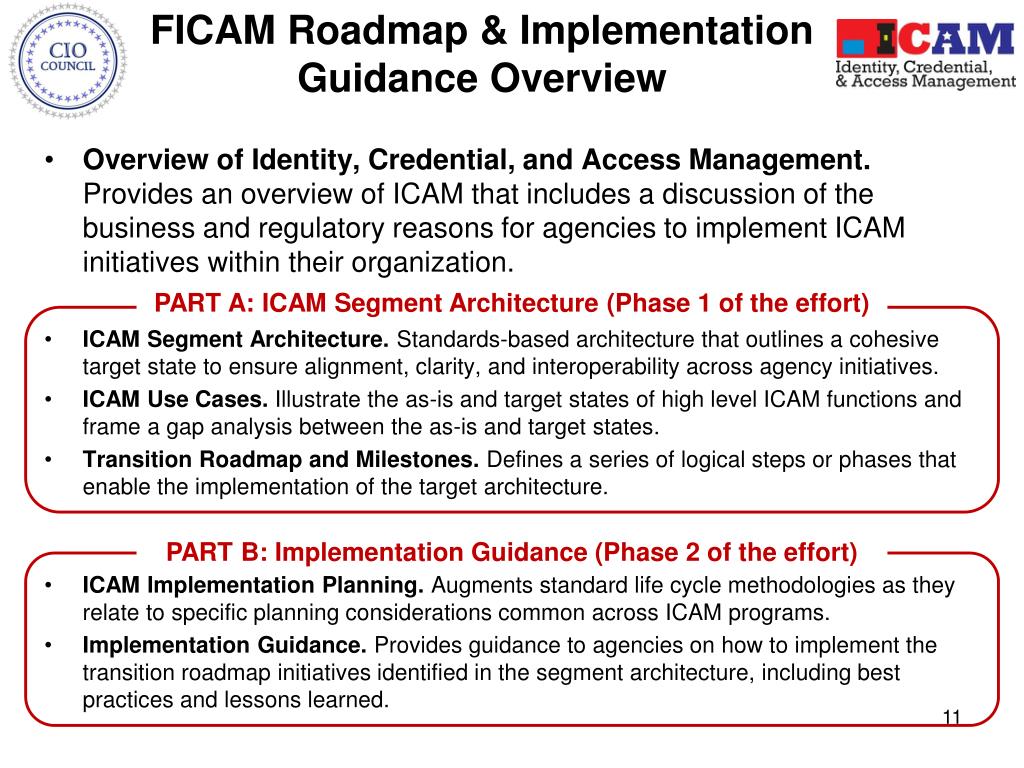
2. Strategic Roadmap Development
ICAM deployments must be carefully planned to avoid disruptions and ensure organizational buy-in. DAG Tech develops a tailored ICAM Roadmap that includes:
- Phased Implementation Planning: Breaking down ICAM deployment into manageable phases.
- Prioritization Matrix: Identifying critical applications, user groups, and systems to onboard first.
- Risk Mitigation Strategies: Preparing for potential technical and organizational risks.
- Interoperability Considerations: Ensuring compatibility with cloud platforms, on-premises environments, and mobile endpoints.
- Governance Frameworks: Establishing clear roles, responsibilities, and escalation paths.
Our roadmaps are actionable, detailed, and tailored to the client’s unique risk tolerance, operational model, and business goals.
3. Federation and Trust Framework Planning
For organizations requiring federated identity solutions, DAG Tech establishes Federation Trust Frameworks to allow secure collaboration across organizational boundaries. We provide:
- Selection and Configuration of Federation Protocols: Including SAML 2.0, OAuth 2.0, OpenID Connect, and WS-Federation.
- Trust Agreements: Facilitating legal and technical trust between entities, ensuring proper policy enforcement.
- Directory Services Integration: Seamlessly connecting LDAP, Active Directory, Microsoft Entra ID (formerly Azure AD), and cloud-based Identity Providers including Okta, Google Cloud Identity, Ping Identity, CyberArk, OneLogin, Auth0, SailPoint, and JumpCloud.
- Cross-Domain Single Sign-On (SSO): Allowing users to access multiple systems with one credential.
Federation solutions must be architected carefully to balance user convenience with risk management — and DAG Tech ensures this balance is achieved.
4. Solution Design and Technology Selection
DAG Tech helps clients choose the right technology stack based on their operational needs and budget. We vet solutions based on:
- Security certifications (e.g., FIPS 140-2, FedRAMP).
- Integration capabilities with enterprise applications (e.g., Salesforce, Microsoft 365, ServiceNow).
- Support for Multi-Factor Authentication (MFA) and biometrics.
- Lifecycle Management Tools for onboarding and offboarding.
- Audit, Reporting, and Analytics functionalities.
Whether the organization prefers COTS (Commercial Off-the-Shelf) solutions, custom builds, or hybrid approaches, DAG Tech ensures the selected technologies are scalable, interoperable, and future-proof.
5. Implementation and Configuration
Our deployment process follows a disciplined, proven methodology:
- Infrastructure Preparation: Setting up secure, redundant environments.
- Directory Synchronization: Ensuring consistent identity records across all connected systems.
- Policy Configuration: Implementing role-based access controls (RBAC), attribute-based access controls (ABAC), or a hybrid model.
- Credential Issuance: Setting up credential enrollment, issuance, and maintenance workflows.
- Federation Enablement: Configuring trust relationships, token signing/encryption, and metadata exchanges.
- User Testing and Validation: Conducting rigorous validation testing before go-live.
Throughout the implementation, we prioritize security hardening, auditability, and scalability.
6. Training, Documentation, and Support
ICAM solutions only deliver full value when users and administrators are confident in operating them. DAG Tech provides:
- End-User Training: Helping employees understand authentication processes, federation use cases, and credential management.
- Administrator Training: Teaching IT teams how to monitor, troubleshoot, and enhance ICAM systems.
- Runbooks and Standard Operating Procedures (SOPs): Delivering detailed, organization-specific documentation.
- Ongoing Support and Optimization: Offering post-deployment support, periodic audits, and continuous improvement services.
We believe that empowering users and administrators alike is critical for long-term ICAM success.
Why Choose DAG Tech?
Experience, Flexibility, and Commitment to Excellence distinguish DAG Tech’s ICAM services. Our approach is methodical yet adaptable, recognizing that no two organizations are identical. We combine:
- Deep technical expertise in identity management technologies and cybersecurity best practices.
- A client-first mindset, focusing on building long-term relationships based on trust and results.
- Full lifecycle support — from initial planning through operational sustainment.
- Agility and responsiveness, adjusting to changes in technology, regulation, and business needs.
Our methodology — refined through years of technology environment modernization projects ensures ICAM deployments are not only successful but sustainable and future-ready.
At DAG Tech, we are proud to guide our clients through every step of the journey. From developing strategic ICAM roadmaps to deploying federated identity solutions, we bring the experience, dedication, and best practices needed to ensure your ICAM program delivers lasting value.
Contact DAG Tech today to learn how we can help you deploy an ICAM consulting and FICAM consulting solution that strengthens security, empowers users, and drives your mission forward.